Protect industrial operations with secure OT network architecture, monitoring, access control and cyber defense for critical infrastructure environments.
OT (Operational Technology) Cyber Security focuses on protecting industrial control systems such as PLCs, RTUs, SCADA and substation automation networks. Gridshield provides solutions that help reduce cyber risk, prevent unauthorized access and ensure secure and stable operations.
Protect critical systems from cyber threats and intrusions.
Track network events and suspicious activity in real-time.
Maintain uptime and stability for mission-critical assets.

Core security capabilities to protect OT environments.
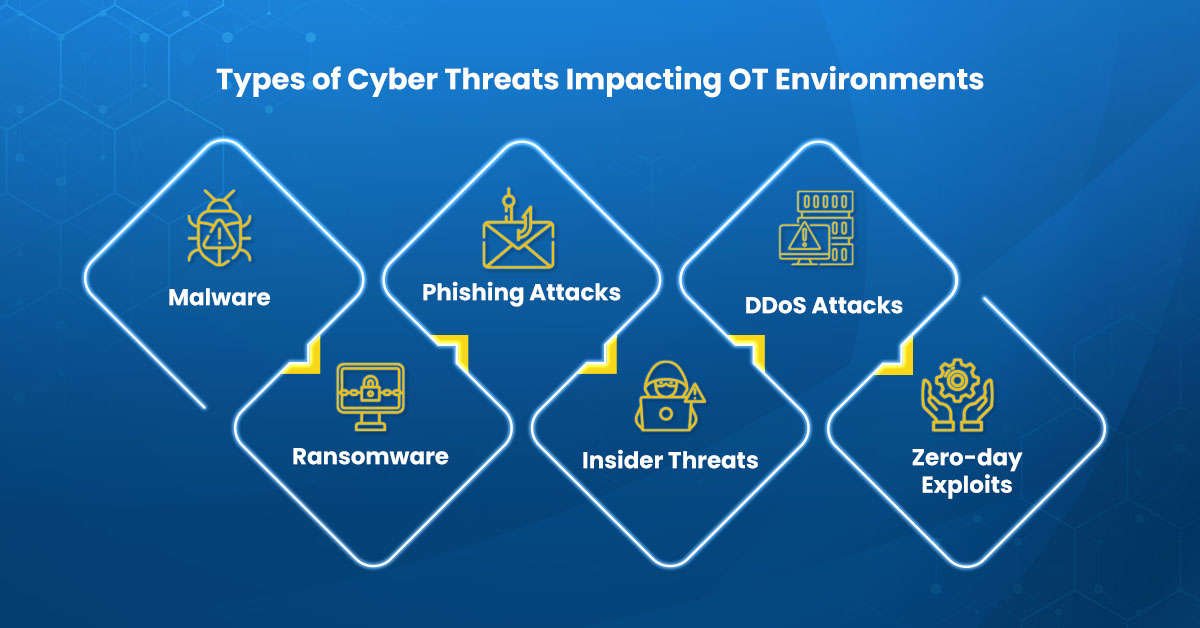
Malware is a type of software designed to disrupt, damage, or gain unauthorized access to a computer system. Malware can enter an OT environment through email attachments, infected USB drives, or vulnerabilities in outdated software.
Ransomware is a type of malware that encrypts files or systems, effectively locking users out of their data until a ransom is paid. Ransomware attacks can cause significant disruptions to OT systems, leading to production downtime and lost revenue.
Phishing attacks are a type of social engineering attack that involves tricking users into giving up their login credentials or other sensitive information. Phishing attacks can be used to gain access to OT systems, compromise user accounts, or steal sensitive data.
Insider threats refer to threats posed by insiders, such as employees or contractors who have access to OT systems. Insider threats can be intentional or unintentional and can result from human error, negligence, or malicious intent.
DDoS attacks involve overwhelming a server or network with traffic, effectively rendering it unusable. DDoS attacks can be used to disrupt OT systems and cause significant downtime.
Zero-day exploits refer to vulnerabilities in software or systems that are unknown to the vendor or security community. Zero-day exploits can be exploited by cybercriminals to gain unauthorized access to OT systems.
Key security areas covered by Gridshield OT Cyber Security.
OT Cyber Security solutions for critical infrastructure and industrial environments.
Gridshield helps industries strengthen OT security with proven solutions, expert guidance and reliable deployment support. We ensure secure communication, monitoring and protection for mission-critical networks.
Contact Gridshield to secure your OT infrastructure and reduce cyber risks.